A 2023 cybersecurity study revealed that 43% of small and mid-sized businesses (SMBs) struggle to understand what security is needed to safeguard their operations and critical organizational data. This “gap in cybersecurity education” leaves SMBs across industries vulnerable to the pervasive threats of cyberattacks.
Relevant to this education gap is a specialized group of professionals who translate the complexity of cyber threats into clarity yet often remain unsung. The guide below explores the vital role of cybersecurity technical writers through the lens of the five W’s: what, why, who, where, and when.
We’ll dissect the distinct yet sometimes overlapping fields of general cybersecurity writing—which focuses on broad awareness and thought leadership—and the highly specialized domain of cybersecurity technical writing.
The latter’s work is indispensable for mitigating risk, ensuring regulatory adherence, and effectively educating a workforce that stands as both a vulnerability and the first line of defense.
What is a Cybersecurity Technical Writer and What Do They Write?
A cybersecurity technical writer (CTW) specializes in transforming complex cybersecurity information into clear, actionable documentation. Unlike general cybersecurity writers who focus on broad awareness or marketing—writing deliverables such as blog posts, website copy, and social media content—CTWs create precise, prescriptive content.
The primary goal of a CTW is to ensure that critical security procedures are understood, enabling effective operations, risk mitigation, and regulatory adherence within an organization. They bridge the gap between highly technical security concepts and the diverse audiences who need to understand and apply those concepts.
With the expertise of a cybersecurity writer, you can ensure your workforce is properly prepared before a cyberattack takes place as well as informed on how to recover in the wake of such an attack.
Notably, CTWs write a number of cybersecurity-related documents, including:
- Security policies. These policies detail rules outlining an organization’s security posture and employee conduct.
- Incident response plans. These plans act as step-by-step guides for handling and recovering from security breaches.
- User manuals. These manuals provide instructions for deploying, configuring, and operating security software and hardware.
- Compliance documentation. These are records demonstrating adherence to regulatory standards like NIST or GDPR.
- Technical reports. These reports include summaries and analyses of security assessments, vulnerabilities, or audit findings.
Why Do Businesses Need Cybersecurity Technical Writers?
Businesses need CTWs because cybersecurity is complex and errors are costly. CTWs translate intricate threats and controls into clear, actionable policies and procedures, ensuring understanding across all employee levels.
This vital clarity drives regulatory compliance, enhances operational efficiency by standardizing processes, mitigates human error risks, and facilitates effective security training, ultimately safeguarding assets and reputation against evolving cyber threats.
Cybersecurity documentation, crafted by CTWs, is the backbone of robust security. Benefits of producing this documentation include:
- Ensuring clarity and understanding. It simplifies complex threats and procedures for all employees, reducing misinterpretation.
- Boosting compliance and audit readiness. It provides auditable evidence of adherence to critical regulations (e.g., GDPR, HIPAA, NIST).
- Enhancing operational efficiency. It standardizes security processes, reducing errors and speeding up incident response.
- Mitigating risk and human error. It codifies best practices, preventing common vulnerabilities arising from human mistakes.
- Facilitating knowledge transfer. It preserves vital security knowledge, which is especially important with staff changes or new technologies.
Who Should Hire a Cybersecurity Technical Writer?
Organizations across virtually all sectors should consider hiring a CTW, especially those with significant digital assets or regulatory obligations.
Specific organizational profiles that can significantly benefit from hiring a CTW include:
- Large enterprises. With complex IT infrastructures and numerous employees, enterprises require robust internal documentation for policies, procedures, and training.
- Government agencies and defense contractors. Strict compliance requirements and classified information, hallmarks of these public sector organizations, necessitate meticulous documentation for security protocols and audits.
- Financial institutions and healthcare providers. Finance and healthcare are heavily regulated industries where data privacy (e.g., HIPAA, GDPR) and financial security demand comprehensive, auditable security documentation.
- Software and cybersecurity product developers. Companies building security tools (e.g., firewalls, SIEMs, antivirus) need CTWs with the understanding of complex cybersecurity concepts to create effective user manuals, API documentation, and technical release notes in this niche vertical.
- Managed security service providers (MSSPs). These organizations deliver security services to clients, which require clear service descriptions, incident reports, and client-specific security policies.
- Consulting firms. Cybersecurity consultants often produce comprehensive reports, risk assessments, and compliance documentation for their clients.
Similarly, specific job roles that inform or rely on the work of CTWs include:
- Chief information security officers (CISOs). CISOs rely on CTWs for policy development, compliance reporting, and strategic communication.
- Security engineers and analysts. Engineers provide the technical input that CTWs translate into actionable guides for implementation and troubleshooting.
- Compliance officers and auditors. Compliance officers depend on CTWs to create and maintain the documentation required for regulatory adherence and successful audits.
- IT administrators. IT admins use CTW-produced manuals and SOPs for daily security operations and system configurations.
- Training and awareness managers. Training managers partner with CTWs to develop clear, engaging security education programs for the entire workforce.
Where Can You Find Cybersecurity Technical Writers?
Finding qualified CTWs requires looking beyond writing skills. Industry knowledge is paramount—they must understand complex security concepts, threats, and compliance frameworks to produce accurate and actionable cybersecurity documentation.
Where can you hire CTWs?
- Freelance platforms like Upwork offer flexibility and access to a global talent pool, ideal for project-based work or specialized needs. However, vetting for deep cybersecurity expertise can be challenging.
- Agencies/consultancies such as Essential Data provide pre-vetted teams and individual technical writers with specialized cybersecurity knowledge, offering scalability and managed projects. This option may be more expensive but reduces hiring overhead (vs. in-house hiring) and increases accountability (vs. freelancer platforms).
- In-house career pages and external job boards offer the deepest integration with your company’s unique systems and culture, fostering long-term knowledge retention. However, this path requires a dedicated recruitment effort to find candidates with both technical writing prowess and cybersecurity acumen via industry-specific job boards (e.g., CyberCoders, Dice), professional organizations (STC, ISC2), or networking.
When Should You Hire a Cybersecurity Technical Writer?
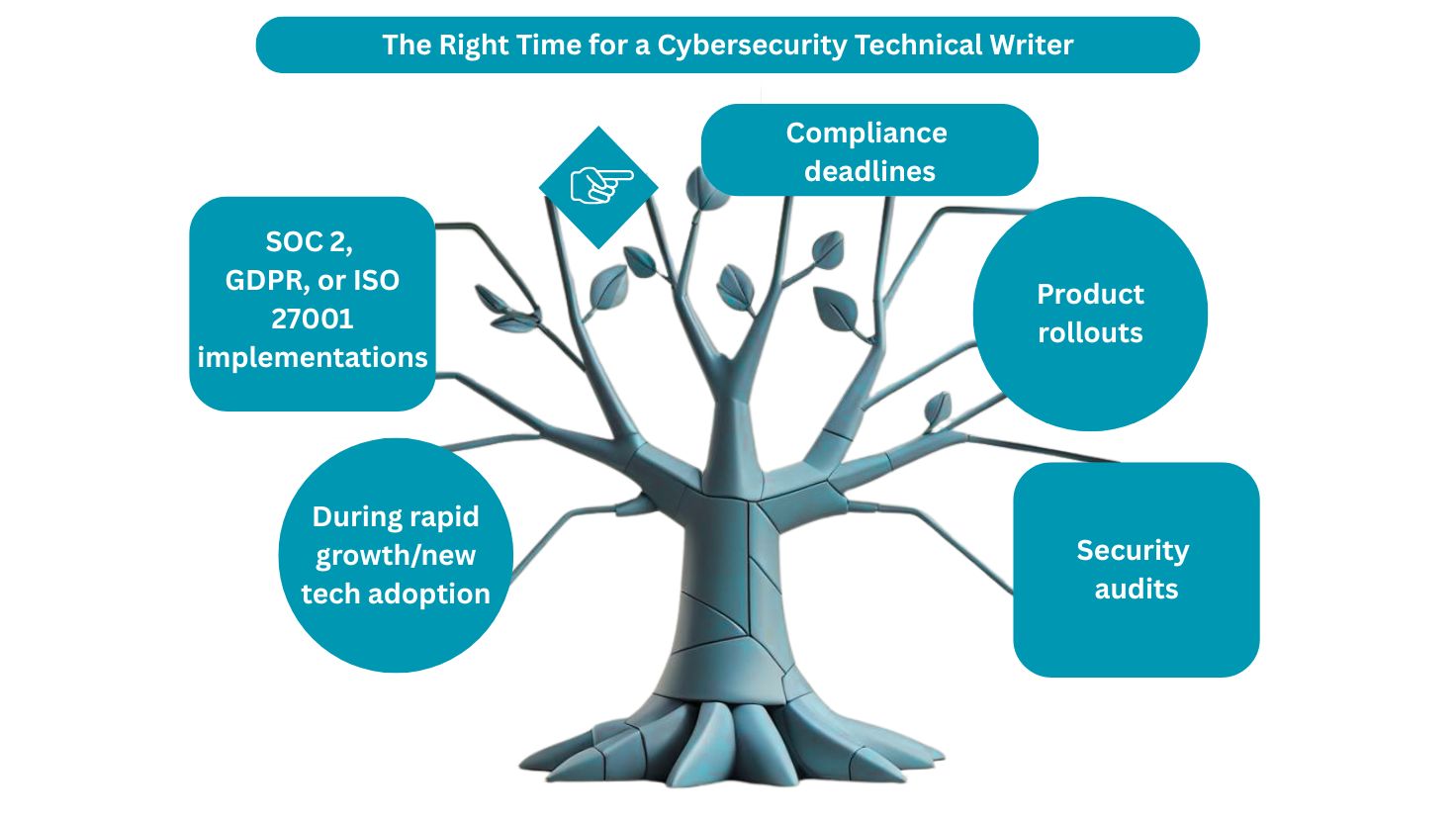
You should strategically hire a CTW proactively to build a resilient security posture, rather than waiting for a crisis to inspire action.
Key situations to bring in a CTW include:
- Compliance deadlines. Well before regulatory deadlines (such as for GDPR, HIPAA, or PCI DSS), CTWs document controls and processes, ensuring readiness for audits.
- Product rollouts. For new security products or features, CTWs create essential user manuals, integration guides, and API documentation for customers and internal teams.
- Security audits. Proactively preparing for internal or external security audits requires comprehensive, up-to-date documentation of security practices and controls.
- SOC 2, GDPR, or ISO 27001 implementations. During the adoption of these frameworks, CTWs are critical for developing the policies, procedures, and evidence required for certification.
- During rapid growth/new tech adoption. As infrastructure expands or new security technologies are integrated, CTWs standardize and document new processes and configurations to maintain control.
Cybersecurity Writing FAQs: The 5 C’s of Cybersecurity
Beyond the five W’s, effective security in this space hinges on the five C’s of cybersecurity: change, compliance, cost, continuity, and coverage. Here, we explore how CTWs directly address each of these critical areas.
Change: How do cybersecurity technical writers ensure security documentation keeps pace with rapidly evolving cyber threats and technology?
CTWs are crucial for translating emerging threats, updated protocols, and new security tools into clear, actionable documentation. They work closely with security teams to ensure policies, procedures, and user guides are continuously updated, reflecting the latest best practices and technical specifications.
Compliance: How do cybersecurity technical writers directly contribute to an organization’s regulatory adherence and audit readiness?
CTWs meticulously create and maintain the precise, auditable documentation required by regulations and frameworks such as GDPR, HIPAA, NIST, or ISO 27001. Their work provides concrete evidence of an organization’s controls and practices, streamlining audits and minimizing risks of non-compliance.
Cost: How can effective cybersecurity documentation by cybersecurity technical writers reduce overall cybersecurity costs for businesses?
By providing clear instructions and standardized procedures, CTWs reduce human error, streamline operations, and minimize time spent on training. This proactive approach helps prevent costly data breaches and significantly reduces potential fines and recovery expenses associated with compliance failures.
Continuity: What role do cybersecurity technical writers play in ensuring business continuity during and after a security incident?
CTWs are essential in developing highly detailed incident response plans, disaster recovery playbooks, and communication protocols. Their clear documentation enables security teams to act swiftly, consistently, and effectively to contain threats, minimize downtime, and restore critical business operations.
Coverage: How do cybersecurity technical writers ensure comprehensive security understanding across diverse audiences within an organization?
CTWs tailor cybersecurity information to provide appropriate coverage for various audiences, from highly technical security engineers to non-technical executives and general employees. They ensure everyone understands their specific security responsibilities and the controls relevant to their role.
Educate and Secure Your Organization with Cybersecurity Technical Writers from EDC

Ultimately, the role of a CTW transcends mere documentation. Theirs is a key role in helping to build a robust, resilient, and comprehensible security ecosystem.
By expertly navigating the five W’s—understanding what CTWs write, why businesses critically need them, who benefits from their unique skills, where to find them, and when to proactively engage them—you can transform the complex security threats and compliance requirements of your organization into actionable intelligence.
This is precisely where specialized consultancies like Essential Data can provide invaluable support. We offer expert cybersecurity technical writing services, bridging the internal resource gap by providing professionals who possess both deep cybersecurity knowledge and superior communication capabilities.
Our consultants have extensive expertise across various types of cybersecurity documentation. Whether you need a single technical writer for an ad-hoc documentation project or a team of consultants to produce a complete line of documents, EDC’s documentation services ensure your organization receives the highest quality policy manuals, procedural guides, other key organizational documents.
Plus, our clients work closely with an engagement manager from one of our 30 local offices for the entire length of your project at no additional cost.
Contact us at (800) 221-0093 or [email protected] to get started.
Read more about: Can Technical Writers Work in Cybersecurity?